10 Penetration Testing Tool Shortlist
Here's my pick of the 10 best software from the 20 tools reviewed.
Our one-on-one guidance will help you find the perfect fit.
With so many different penetration testing tools available, figuring out which is right for you is tough. You know you want to identify and address security gaps before they can be exploited but need to figure out which tool is best. I've got you! In this post I'll help make your choice easy, sharing my personal experiences using dozens of different penetration testing software with various teams, with my picks of the best penetration testing tools.
Why Trust Our Penetration Testing Tool Reviews?
We’ve been testing and reviewing penetration testing tools since 2021. As QA software testers ourselves, we know how critical and difficult it is to make the right decision when selecting software.
We invest in deep research to help our audience make better software purchasing decisions. We’ve tested more than 2,000 tools for different use cases and written over 1,000 comprehensive software reviews. Learn how we stay transparent & our penetration testing tools review methodology.
The Best Penetration Testing Tools Summary
| Tools | Price | |
|---|---|---|
| New Relic | From $49/user/month | Website |
| Intruder | From $196/month/application | Website |
| Astra Pentest | From $199/month | Website |
| Acunetix | Pricing available upon request | Website |
| AppTrana | $99/month/app | Website |
| Core Impact | Starts at $9,450 USD/year for the Basic package | Website |
| Metasploit | Pricing available upon request | Website |
| Aircrack-ng | No price details | Website |
| Burp Suite | Starts at $6,995/ year | Website |
| Nessus | From $473.90/month for a license (billed annually) | Website |
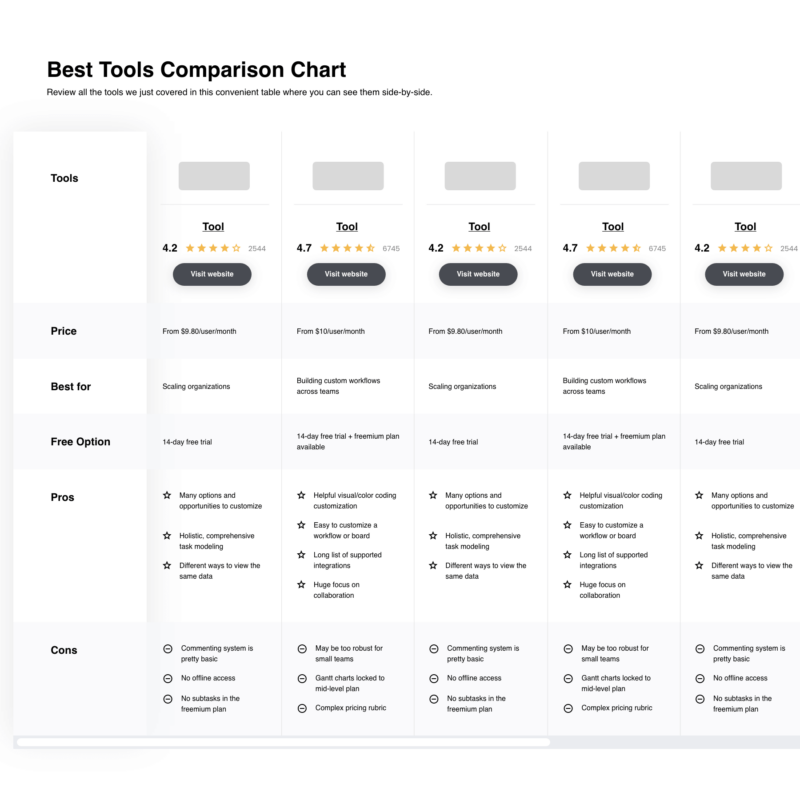
Compare Software Specs Side by Side
Use our comparison chart to review and evaluate software specs side-by-side.
Compare SoftwareHow To Choose Penetration Testing Tools
With so many different penetration testing tools available, it can be challenging to make decisions on what tools are going to be the best fit for your needs.
As you're shortlisting, trialing, and selecting penetration testing tools, consider:
- What problem are you trying to solve - Start by identifying the penetration testing tool feature gap you're trying to fill to clarify the features and functionality the tool needs to provide.
- Who will need to use it - To evaluate cost and requirements, consider who'll be using the software and how many licenses you'll need. You'll need to evaluate if it'll just be the QA software testers or the whole organization that will require access. When that's clear, it's worth considering if you're prioritizing ease of use for all or speed for your penetration testing tool power users.
- What other tools it needs to work with - Clarify what tools you're replacing, what tools are staying, and the tools you'll need to integrate with, such as other testing tools, automation tools, or bug tracking software. You'll need to decide if the tools will need to integrate together or if you can replace multiple tools with one consolidated penetration testing tool.
- What outcomes are important - Consider the result that the software needs to deliver to be considered a success. Consider what capability you want to gain or what you want to improve and how you will be measuring success. For example, an outcome could be the ability to get greater visibility into performance. You could compare penetration testing tool features until you’re blue in the face but if you aren’t thinking about the outcomes you want to drive, you could be wasting a lot of valuable time.
- How it would work within your organization - Consider the software selection alongside your workflows and delivery methodology. Evaluate what's working well, and the areas that are causing issues that need to be addressed. Remember every business is different — don’t assume that because a tool is popular that it'll work in your organization.
Best Penetration Testing Tools Reviews
Here’s a brief description of each penetration testing tool to showcase each tool’s best use case, some noteworthy features, and screenshots to give a snapshot of the user interface.
New Relic is all about application performance management (APM). It's a tool for those who need to monitor and manage the performance of their software applications. It's got a lot of great features that make it a great choice for quality assurance (QA) and penetration testing.
It's got a super comprehensive suite of features that make it easy to monitor, troubleshoot, and optimize your applications. Plus, it's got an intuitive interface that makes it easy to get the hang of, even if you're not a tech whiz.
One of the things I love about New Relic is its real-time analytics. It gives you instant insights into how your application is performing, which is super helpful when you're trying to identify and fix issues. It's also got a great alert system that notifies you when something's not right, so you can jump on it right away.
Key features include backend monitoring, Kubernetes monitoring, mobile monitoring, model performance monitoring, infrastructure monitoring, log management, error tracking, network monitoring, vulnerability management, and browser monitoring.
Integrations include over 500 apps, like AWS, Google Cloud, and Microsoft Azure, CI/CD tools like Jenkins, CircleCI, and Travis CI, communication tools like Slack and PagerDuty, and other monitoring and analytics tools like Grafana, Datadog, and Splunk. It also has an API you can use to build custom integrations.
New Relic costs from $49/user/month and offers a free plan for 1 user and 100 GB/month of data ingest.
Intruder is a cloud-based security scanning platform designed to identify and help remediate cyber security weaknesses in your digital infrastructure. It stands out for its proactive approach to vulnerability scanning, aiming to detect and address security issues before they are exploited by malicious actors.
What makes the software different is the comprehensive remediation instructions that accompany scan results. These not only identify issues but also guide you through the resolution process. It offers a proactive approach to vulnerability scanning, keeping you ahead of potential threats.
The software integrates natively with Slack, Microsoft Teams, Jira, Github, and Gitlab. Other integrations can be accessed through Zapier and API.
Paid plans start from $196 per month, per application. A 14-day free trial is also available.
Best for vulnerability scanning and pentesting for 9300+ test cases
Astra Pentest offers a developer-oriented pentesting solution that includes both an automated vulnerability scanner and expert manual testing to help eliminate any false positives. This platform conducts over 9,300 security checks in compliance with multiple standards including OWASP, SANS, HIPAA, ISO, GDPR, and SOC to ensure full testing coverage. Additionally, the software's AI-driven chatbot provides developers with detailed guidance on how to address security vulnerabilities.
The platform features a unified dashboard that promotes effective collaboration between development teams and security professionals. It supports real-time consultation with security experts and focuses on continuous scanning. The vulnerability scanning and pentesting tools are capable of evaluating modern web applications, including single-page apps, progressive web apps, and logged-in pages. Astra also issues a verifiable security certificate to enhance credibility with clients and partners.
Astra integrates with platforms such as Jira, Slack, GitLab, and GitHub.
The cost of Astra starts at $199.00 USD per month for the Scanner package.
Acunetix is a penetration testing tool that is easy to use, and provides an array of features accessible to any level of a development team. Acunetix provides a quick analysis that can identify high risk vulnerabilities, as well as the ability to send different types of reports to various levels from board member to developer, tailored especially for the recipient.
Acunetix provides the ability for continuous scanning, allowing you to schedule regular scans of targets which checks for vulnerabilities in your infrastructure repeatedly. This allows you to have continuous security awareness of your organization’s vulnerability level. The feature also allows you to pause the scan at any time.
Acunetix integrates with issue trackers such as Jira, Bugzilla and Mantis.
Acunetix offers customized pricing upon request.
AppTrana
Best web application firewall (WAF) and risk-based security solution
AppTrana is a web application firewall (WAF) used for penetration testing, behavioral-based DDoS protection, mitigating bot attacks, and defending against the OWASP top 10 vulnerabilities. AppTrana is employed by security-conscious companies across myriad industries, such as Axis Bank, Jet Aviation, Niva Health Insurance, and TRL Transport.
AppTrana is a fully managed security solution, which means that their web security expert team takes on the analyzing and updating of security policies so you don't have to. Higher-level accounts will get a named account manager to assist them; the highest subscription level comes with quarterly service reviews (highly recommended!).
Key features include unlimited application security scanning, manual pen-testing of applications, managed CDN, false positive monitoring, custom SSL certificates, and risk-based API protection. Their website is packed full of detailed feature explanations as well as a blog, learning center, whitepapers, infographics, and datasheets, so I highly recommend you take a look around for yourself.
AppTrana costs from $99/month/app and comes with a free 14-day trial.
Core Impact is a comprehensive penetration testing tool that allows you to exploit weaknesses in the security of your applications, and increase productivity. The tool provides an easy and clean user interface, as well as the ability to execute rapid penetration tests. This allows you to discover, test and report more efficiently.
Core Impact provides a feature for replicating multi-staged attacks, which allows you to pivot your pen tests across various systems, devices and applications. The feature allows you to configure various tests and execute them all at once. Another feature of Core Impact is the ability to install an agent on the server through SSH and SMB, making white box testing more effective.
The cost of Core Impact starts at $9,450 USD per year for the Basic package. The tool also offers a free trial.
Metasploit is a penetration testing tool that identifies system weaknesses and attempts to exploit them, allowing you to isolate and demonstrate the weakness, and allow for remediations. The tool also works across multiple computer systems such as Windows, Linux and Mac OS X, and can be used across devices.
Metasploit provides the ability to automate manual tests and exploits, allowing you to minimize your team’s time spent on creating manual tests and scans. The tool boasts a large exploit database with new additions regularly, and is extremely intuitive, making it easy for you and your team to implement. Metasploit also has a large community support system.
Metasploit integrates with tools such as Kali Linux and Dradis.
The cost of Metasploit starts at $2,000 per year. The tool also offers a free version.
Aircrack-ng is a security testing tool that allows you to complete WiFi auditing and security assessments of your wireless network. The tool allows you to carry out security testing such as checking WiFi cards and driver capabilities. Aircrack-ng also allows you to packet capture and export the data to text files so you can process further using third party tools.
Aircrack-ng provides a robust attacking feature that allows you to simulate attacks on your wireless network. The tool allows you to perform replay attacks and de-authentication, as well as set up fake access points. Aircrack-ng also allows you to perform attacks on WEP and WPA PSK.
Aircrack-ng is fully open source and free to use.
Burp Suite is a penetration testing tool that allows you to improve your cyber security protocols with the use of a fully fleshed out toolkit. The tool boasts an array of features such as the Burp Intruder which allows you to automate customized cyber attacks against your applications, and Burp Repeater which allows you to manipulate and reissue individual HTTP requests manually.
Burp Scanner also has a passive scanning feature that allows you to divide the checks performed into active and passive checks. This allows you to set the targets and scopes, and cover areas that are easily missed. The tool also allows you to conduct active scans, ensuring that the entirety of your application is covered.
Burp Suite integrates with tools such as Jenkins and TeamCity.
The cost of Burp Suite starts at $6,995 per year. The tool also offers a free trial.
Nessus is a penetration testing tool that allows you to complete vulnerability assessments of your web application and operating systems. The tool allows you to easily identify and fix vulnerabilities, including software flaws, malware and missing patches. Nessus can operate across a variety of systems and devices.
Nessus provides the ability to perform both credential and non credentialed scans, allowing you to find more depth vulnerabilities. This ensures that you have full test coverage of your operating system, and are catching every security flaw within your application. The tool also covers network devices such as endpoints, servers and virtualization platforms.
Nessus integrates with tools such as Google Cloud, Microsoft Azure and ServiceNow.
The cost of Nessus starts at $4,719.13 USD per year. The tool also offers a 7-day free trial.
Other Penetration Testing Tools
Here are a few more that didn’t make the top list.
- Kali Linux
Best pentesting with live USB mode for portable use
- Invicti
Best to configure pre-set scan profiles for less experienced users
- W3af
Best open source web application cyber security scanner
- BreachLock
Best for comprehensive and scalable pen testing
- UnderDefense
Best for human-led penetration testing
- SQLMap
Best open source penetration testing tool used to detect and exploit SQL injection flaws
- NMap
Best free and open source utility for network discovery and security auditing
- Indusface WAS Free Website Security Check
Best for vulnerability protection with on demand manual testing
- John the Ripper
Best free password cracking tool that monitors your password security and also operates as a password recovery tool
- Cain & Abel
Best free password cracking tool that uses brute force to assess the strength of your passwords
Related Penetration Testing Tool Reviews
If you still haven't found what you're looking for here, check out these tools closely related to penetration testing tools that we've tested and evaluated.
- Automation Testing Tools
- Software Testing Tools
- Test Management Tools
- CI/CD Tools
- Incident Management Software
- Code Review Tools
Selection Criteria For Penetration Testing Tools
Penetration testing tools are instrumental in identifying vulnerabilities before they can be exploited maliciously. My selection criteria are deeply rooted in comprehensive personal trials and thorough research, ensuring that the chosen tools align well with specific use cases and buyer requirements.
Core Penetration Testing Tool Functionality: 25% of total weighting score
To be considered for inclusion on my list of the best penetration testing tools, the solution had to support the ability to fulfill common use cases such as:
- Network and application layer testing
- Compliance assessment and reporting
- Identification and exploitation of vulnerabilities
- Integration with other security tools
- User behavior simulations
Additional Standout Features: 25% of total weighting score
In distinguishing exceptional tools, I look for:
- Advanced automation capabilities to streamline testing processes.
- Unique analytical features that provide deeper insights into vulnerabilities.
- Customization options to tailor the tool to specific organizational needs.
- Scalability to accommodate growing business requirements.
- Innovative approaches to threat detection and analysis.
Usability: 10% of total weighting score
Usability is key. I prioritize tools that balance advanced capabilities with user-friendly interfaces, including:
- Intuitive dashboard and visualization features.
- Clear guidance and documentation.
- Minimal learning curve with straightforward operation.
Onboarding: 10% of total weighting score
Effective onboarding determines how swiftly teams can leverage the tool's full potential, hence I assess:
- Availability of training resources like videos or tutorials.
- Quality of onboarding support and materials.
- Ease of setting up and integrating the tool into existing workflows.
Customer Support: 10% of total weighting score
Robust customer support ensures that any issues are promptly addressed:
- Availability of multiple support channels.
- Responsiveness and expertise of the support team.
- Availability of community support or forums.
Value For Money: 10% of total weighting score
Cost-effectiveness is crucial without compromising on key functionalities:
- Transparent pricing models.
- Flexibility in terms of scalable features and payment plans.
- Overall ROI considering the tool's impact on security posture.
Customer Reviews: 10% of total weighting score
Peer reviews provide invaluable insights into real-world tool performance:
- Overall satisfaction ratings.
- Feedback on specific features and usability.
- Comparative analysis with similar tools in the market.
My selection process for penetration testing tools is rigorous and multifaceted, focused on aligning with buyers' needs and pain points while ensuring comprehensive functionality and excellent user experience. This ensures that organizations can effectively manage and execute their software tests, maintaining a robust security posture.
Trends In Penetration Testing Tools For 2024
Penetration testing tools are rapidly evolving to accommodate the increasing complexity of cyber threats and the growing sophistication of technology infrastructure. These trends not only reflect the advancements in technology but also underline the shifting priorities within the field of cybersecurity.
- Enhanced Automation and Integration: Automation in penetration testing is advancing rapidly, streamlining the testing process, reducing manual efforts, and increasing efficiency. The integration of these tools with other systems like CI/CD pipelines, issue trackers, and security operation centers is becoming more prevalent, enhancing real-time response and remediation capabilities.
- AI and Machine Learning Incorporation: The incorporation of AI and machine learning algorithms is becoming a standout feature, enabling more intelligent and adaptive testing. These technologies help in identifying patterns, predicting potential vulnerabilities, and providing proactive security measures, which are critical in managing complex and dynamic environments.
- Cloud and Container Security: With the adoption of cloud services and containerization, penetration testing tools are expanding their capabilities to address these specific environments. The focus is on providing comprehensive testing that covers multi-cloud environments, container orchestration platforms, and serverless architectures, addressing the unique challenges these technologies present.
- Compliance and Reporting: As regulatory requirements evolve, the need for robust compliance and reporting features is more critical than ever. Tools are focusing on generating detailed, understandable, and actionable reports that align with various compliance standards, helping organizations maintain regulatory adherence.
Penetration testing tools are moving towards greater automation, embracing AI and ML, expanding to cover new technological frontiers like the cloud and containers, focusing on user experience, and aligning closely with compliance needs. For QA software testers, staying on top of these trends is crucial in selecting tools that will effectively address the evolving landscape of cybersecurity challenges.
What are Penetration Testing Tools?
Penetration testing tools are software used to assess the security of computer systems, networks, and web applications. They simulate cyberattacks to identify and exploit vulnerabilities, testing the effectiveness of security measures. These tools are used by security professionals to discover weaknesses in IT infrastructures, mimicking the techniques of potential attackers.
The benefits and uses of penetration testing tools include enhancing the security of systems by proactively uncovering and addressing vulnerabilities. They help in preventing unauthorized access and data breaches by identifying weaknesses before they can be exploited by real attackers. These tools are essential for maintaining strong cybersecurity defenses, ensuring compliance with security standards, and protecting sensitive information. They provide valuable insights into security risks, enabling organizations to make informed decisions about strengthening their security posture.
Features Of Penetration Testing Tools
Penetration testing tools simulate real-world attacks to ensure that organizations can understand and mitigate potential risks. Here, I outline the most important features to consider when selecting penetration testing tools to execute software tests effectively.
1. Comprehensive Vulnerability Scanning: This feature allows the tool to detect a wide range of vulnerabilities. It's crucial because it ensures that the software test covers as many potential security issues as possible, allowing for a thorough risk assessment.
2. Automated Exploit Execution: Automating the execution of known exploits saves time and increases efficiency. This feature is important because it allows testers to quickly identify and focus on exploitable vulnerabilities within the system.
3. Customizable Testing Options: Flexibility in configuring tests to suit specific environments or requirements is vital. It enables testers to tailor the testing process to the unique aspects of the software or system, ensuring more relevant and accurate results.
4. Detailed Reporting and Logging: Providing detailed insights and records of all identified vulnerabilities and testing actions is essential. It helps teams understand the risks, prioritize fixes, and track testing progress over time.
5. Integration Capabilities: The ability to integrate with other security tools and systems streamlines the testing process. This feature is crucial for ensuring that the penetration testing tool can work seamlessly within the existing security ecosystem.
6. User-Friendly Interface: An intuitive interface ensures that testers can use the tool effectively, regardless of their experience level. It is important for facilitating smooth and efficient testing processes.
7. Regular Updates and Support: Keeping the tool updated with the latest exploit databases and testing methodologies is crucial. It ensures that the tool remains effective against evolving threats and provides ongoing value.
8. Multi-Platform Support: The ability to test across various operating systems and environments is essential. This feature ensures that the tool can provide comprehensive coverage, regardless of the technology stack.
9. Network and Web Application Testing: Supporting both network and web application penetration testing ensures that the tool can address a broad range of security concerns. It is crucial for comprehensive testing across different layers of an organization's infrastructure.
10. Speed and Efficiency: Fast and efficient testing allows for quicker identification of vulnerabilities and reduces the overall testing cycle time. This feature is important for keeping pace with rapid development cycles and ensuring timely vulnerability management.
Selecting the right penetration testing tool is a strategic decision that significantly influences the effectiveness of software testing efforts. By focusing on these key features, organizations can choose tools that provide thorough, efficient, and insightful testing, enabling them to identify and address vulnerabilities proactively.
Benefits Of Penetration Testing Tools
Penetration testing tools offer a proactive approach to identifying and addressing vulnerabilities, thereby reducing the risk of unauthorized access or data breaches. Here, I highlight five primary benefits these tools provide to users and organizations, helping potential software testing tool buyers understand their importance.
1. Enhanced Security Posture: Penetration testing tools help identify and remediate vulnerabilities before attackers can exploit them. This proactive approach significantly strengthens an organization's defenses, making it more resilient against cyber threats.
2. Cost Savings: By identifying and addressing vulnerabilities early, these tools can prevent costly data breaches and associated penalties. They help organizations save money in the long term by avoiding the repercussions of security incidents.
3. Compliance Assurance: Many industries have stringent regulatory requirements regarding data protection and cybersecurity. Penetration testing tools aid in maintaining compliance with these regulations, reducing the risk of legal issues and fines.
4. Reputation Protection: Maintaining customer trust is crucial for any business. By ensuring that vulnerabilities are identified and addressed promptly, penetration testing tools help protect an organization's reputation and maintain customer confidence.
5. Informed Decision-Making: Detailed reports from penetration tests provide valuable insights into an organization's security landscape. These insights guide strategic decisions, resource allocation, and investment in security measures, ultimately enhancing overall business resilience.
Costs & Pricing For Penetration Testing Tools
Penetration testing tools offer various features and capabilities, tailored to suit different needs and budgets. Below, I outline typical plan options you might encounter, providing insights into what each includes and its average cost, helping you make an informed decision based on your organization's requirements.
Plan Comparison Table For Penetration Testing Tools
| Plan Type | Average Price | Common Features Included |
|---|---|---|
| Basic | $0 - $500/month | Limited scans, basic reporting, community support |
| Standard | $500 - $1,500/month | Automated scans, compliance reporting, email support |
| Premium | $1,500 - $5,000/month | Full-range scans, advanced reporting, phone support |
| Enterprise | $5,000+/month | Customizable scans, dedicated support, integration capabilities |
| Free | $0 | Access to limited features, community forums, basic detection capabilities |
When choosing a plan, consider both your organization's specific security needs and budget. Starting with a basic or free plan can provide a good introduction, while premium or enterprise options offer more advanced features for comprehensive security assessments. Always assess the balance between cost and the level of security assurance you require.
Penetration Testing Tool Frequently Asked Questions
Here are a few questions I frequently hear about penetration testing.
What are the types of penetration testing tools?
Penetration testing tools are diverse, each designed to address specific aspects of security assessment within various environments and applications. Understanding the different types allows organizations to select tools that best fit their security testing needs. Here are the primary types of penetration testing tools:
- Network Penetration Testing Tools: These tools focus on identifying vulnerabilities within network infrastructures, including servers, network devices, and endpoints. They can detect open ports, misconfigured firewalls, and other network-related vulnerabilities.
- Web Application Penetration Testing Tools: These tools are specialized for assessing the security of web applications. They identify issues like SQL injection, cross-site scripting, and other vulnerabilities that could be exploited via the web interface.
- Wireless Penetration Testing Tools: With the growing use of wireless networks, these tools help identify vulnerabilities in wireless communication protocols, including Wi-Fi networks. They can detect issues like weak encryption, rogue access points, and other security flaws in wireless configurations.
- Social Engineering Penetration Testing Tools: These tools simulate attacks that leverage human interaction, such as phishing or baiting, to identify how well an organization’s employees adhere to security policies and training.
- Physical Penetration Testing Tools: These are used to assess the physical security measures of an organization, identifying vulnerabilities that could allow unauthorized physical access to sensitive areas or information.
- Mobile Penetration Testing Tools: As mobile devices become integral to business operations, these tools assess the security of mobile applications and platforms, identifying vulnerabilities specific to mobile operating systems and apps.
By choosing the appropriate type of penetration testing tool, organizations can effectively assess their security posture across different layers of their IT environment, identifying vulnerabilities before they can be exploited by malicious actors.
Who uses penetration testing tools?
Penetration testing tools are used by a variety of professionals and organizations to assess and enhance their cybersecurity measures. Here are some of the primary users:
- Security Analysts and Penetration Testers: These are the primary users of penetration testing tools. They are skilled professionals who specialize in conducting tests to identify and exploit vulnerabilities in systems, networks, and applications.
- IT Security Teams: Within an organization, IT security teams use these tools to continuously assess and improve the security of their IT infrastructure. This proactive approach helps in identifying vulnerabilities before they can be exploited.
- Ethical Hackers: These individuals are hired to deliberately attack an organization’s systems, with permission, to find and fix security vulnerabilities. They use penetration testing tools to simulate real-world attacks.
- Cybersecurity Consultants: Consultants might use these tools to provide assessments and improvements for their clients’ security systems. They help organizations understand their security posture and recommend necessary enhancements.
- Compliance Auditors: Some regulations and standards require organizations to conduct regular penetration tests. Auditors use these tools to verify that the organizations are compliant with the relevant cybersecurity standards.
- Researchers and Academics: In the cybersecurity research field, academics and researchers use penetration testing tools to study security vulnerabilities, attack methods, and defense mechanisms.
- Organizations with Sensitive Data: Enterprises that handle sensitive data, such as financial institutions, healthcare organizations, and government agencies, use these tools to ensure their data remains secure against cyber threats.
By using penetration testing tools, these various users can identify security weaknesses and implement stronger defenses, thereby protecting their systems and data from malicious attacks.
What Other Testing Resources Do I Need?
If you’re looking for penetration testing tools, these resources may also help you:
Conclusion
Cyber crime continues to spike worldwide due to the increased accessibility of online resources and the increase in the amount of companies moving their businesses into remote working. I hope the tools that I have covered in this article will help you make an informed decision about the best route to take for your team and your business in ensuring your cyber security is locked up.
For more articles like this, be sure to subscribe to The QA Lead newsletter.





















