10 Best Vulnerability Scanning Software Shortlist
Here's my pick of the 10 best software from the 19 tools reviewed.
With so many different vulnerability scanning software available, figuring out which is right for you is tough. You know you want to proactively discover and address security gaps before they can be exploited but need to figure out which tool is best. I've got you! In this post I'll help make your choice easy, sharing my personal experiences using dozens of different vulnerability scanning tools with a variety of teams and projects, with my picks of the best vulnerability scanning software.
What Is Vulnerability Scanning Software?
Vulnerability scanning software is a tool used in cybersecurity to detect security weaknesses and vulnerabilities in computer systems, networks, and applications. It systematically scans these systems to identify potential vulnerabilities like outdated software, missing patches, and configuration flaws, providing a security assessment of the scanned environment.
The benefits and uses of vulnerability scanning software include enhancing an organization's cybersecurity by proactively identifying vulnerabilities that could be exploited by cyber attackers. It helps in prioritizing security risks and guides the remediation process to fix detected vulnerabilities. This software is essential for maintaining compliance with various security standards and regulations, ensuring the organization's digital infrastructure is safeguarded against potential threats. By regularly scanning systems, it supports a robust security posture and builds trust with customers and stakeholders.
Overviews Of The 10 Best Vulnerability Scanning Software Solutions
Here’s a brief description of each vulnerability scanning system to showcase each tool’s best use case, some noteworthy features, and screenshots to give a snapshot of the user interface.
Intruder is a cloud-based vulnerability scanner that aims to help businesses of all sizes discover security weaknesses in their online systems. The tool provides continuous monitoring of the network to identify vulnerabilities and reduce the attack surface.
Intruder provides a proactive security monitoring service, which includes regular scans to detect new threats as they emerge. Its network vulnerability scanning checks for over 10,000 vulnerabilities automatically. The tool then prioritizes the results to help focus on the issues that matter most and provide clear information on how to fix them.
Integrations are natively available with Slack, MS Teams, Jira, Github, and Gitlab. Other integrations can be accessed through Zapier and API.
Intruder costs from $196/month/application. A 14-day free trial is also available.
Astra is a comprehensive security scanning platform that provides penetration testing services for web applications, cloud security, mobile apps, APIs, network security, and blockchain. Its platform is designed to be accessible to both executives and developers.
As a vulnerability scanning software, Astra especially excels in continuous web app security testing with pentest functionalities that provide an intelligent vulnerability scanner to perform over 8000 tests. This includes checks for known CVEs, OWASP Top 10, SANS 25, and compliance with standards like ISO 27001, HIPAA, SOC2, or GDPR.
The platform also features SMART reporting with a dashboard for tracking progress, managing teams, and offering detailed recommendations for fixing vulnerabilities, along with a publicly verifiable security certificate to demonstrate a commitment to security. Integrations include GitHub, GitLab, Jenkins, Bitbucket, Azure, CircleCI, Slack, Jira, and more.
Best for identifying potential security weaknesses across an organization's network
ESET PROTECT Complete provides a robust cybersecurity framework designed to protect businesses from a wide range of digital threats. This solution offers a suite of tools including endpoint protection, cloud sandboxing, and data encryption, aiming to deliver a secure, manageable, and comprehensive defense mechanism against malware, ransomware, and phishing attacks.
As a vulnerability scanning software, ESET PROTECT Complete excels in identifying and addressing potential security weaknesses across an organization's network. It provides detailed vulnerability reports, highlighting areas of concern and recommending actionable steps to mitigate risks. Its scanning engine is both thorough and efficient, ensuring minimal disruption to operational activities while maintaining a high level of security awareness.
ESET PROTECT Complete natively integrates with a variety of tools, including ESET Endpoint Security, ESET Endpoint Antivirus, ESET Security Management Center, ESET Dynamic Threat Defense, ESET Secure Authentication, ESET File Security for Microsoft Windows Server, ESET Mail Security for Microsoft Exchange Server, ESET Full Disk Encryption, Microsoft Active Directory, and SIEM tools.
ESET PROTECT Complete offers pricing upon request + a 30-day free trial.
Qualys
Information security solution that provides deep visibility into global assets
Qualys analyzes misconfigurations and threats across your global tech environment with six sigma accuracy. The system provides real-time alerts on zero-day vulnerabilities, compromised assets, and network irregularities. You can quarantine compromised assets with a single click, buying you more time to investigate and contain an attack.
To protect your IT environment, you need to know which assets are connected to your network. Qualys’ free Global AssetView application helps security teams accomplish this by automatically identifying all known and unknown assets on a network. You can quickly grab detailed information about each asset, including installed software, running services, and vendor lifecycle information. The application also helps with asset organization, enabling teams to categorize assets into product families with custom tagging.
Qualys supports native integrations with AWS, Azure, and Google Cloud.
Pricing is based on several factors, including the number of user licenses, Qualys Cloud Platform Apps, internal web applications, and IP addresses your team will be utilizing.
Acunetix
Provides comprehensive threat detection with blended DAST + IAST approach
Acunetix is a penetration testing tool that is easy to use, and provides an array of features accessible to any level of a development team. Acunetix provides a quick analysis that can identify high risk vulnerabilities, as well as the ability to send different types of reports to various levels from board member to developer, tailored especially for the recipient. Acunetix provides the ability for continuous scanning, allowing you to schedule regular scans of targets which checks for vulnerabilities in your infrastructure repeatedly. This allows you to have continuous security awareness of your organization's vulnerability level. The feature also allows you to pause the scan at any time. Acunetix integrates with issue trackers such as Jira, Bugzilla and Mantis. Acunetix offers customized pricing upon request.
Free Windows security scanner with built-in remediation guidance
Microsoft Baseline Security Analyzer (MBSA) is a free vulnerability scanner designed for small to medium-sized businesses. QA analysts can scan local and remote systems to identify common IIS and SQL administrative vulnerabilities, like weak passwords or too many admin accounts and missing security updates.
Users can scan multiple computers by domain or IP address range. After each scan, MBSA provides a detailed report on which systems were scanned, the vulnerabilities found, and step-by-step instructions on fixing each issue. QA analysts can quickly access security reports for each computer from MBSA’s GUI. Reports older than seven days will indicate a new scan should be performed, ensuring your team maintains a regular cadence of security monitoring.
MBSA is compatible with Windows Server 2008 R2, Server 2003, Server 2008, Vista, XP, and Windows 2000.
Invicti
Automated web application scanner with highly accurate vulnerability location
Invicti is a simple to use web application scanner built for enterprise security teams. Security analysts gravitate to Invicti because of its ability to automate nearly all pre-and post-scan tasks. Invicti also leads the industry in scan accuracy based on independent benchmark tests performed against other vulnerability scanning tools. The platform blends dynamic and interactive scanning, helping teams discover actual vulnerabilities and fewer false positives.
Producing secure code is how you prevent vulnerabilities. Invicti helps software teams accomplish this with its vulnerability location feature. Security analysts can see the exact lines of code that need fixing when Invicti’s IAST sensor is deployed. As a result, developers receive the information they need to fix software issues faster.
Invicti was designed to embed security into your entire software development lifecycle with more than 50 integrations. Development teams can connect Invicti to Jenkins, Jira, GitLab, and other leading CI/CD tools.
Pricing is available upon request.
Tenable’s Cyber Exposure Platform helps businesses protect every corner of their web environment, including applications, data, and cloud infrastructure. Tenable is known for developing Nessus, a fully portable vulnerability scanner. Nessus offers comprehensive remote and local scanning capabilities while maintaining low operating costs.
IT teams can scan a broad range of network devices, including firewalls, routers, switches, printers, and storage to identify security vulnerabilities. Nessus also covers cloud applications and instances, such as Salesforce and AWS. Your team can detect various threats, including viruses, malware, backdoors, and web services linking to malicious content.
Prioritizing vulnerabilities is simple with Tenable’s Top 10 Reporting, which assigns a Vulnerability Priority Rating (VPR) to the most critical threats detected during a scan. VPR calculations are based on several criteria, including the vulnerability’s age, the exploit code’s maturity, and how many of your products are affected.
Tenable integrates with Splunk, ARCON, CyberArk, and many other security operations platforms.
Pricing for Nessus Pro starts at $3,390 for a one-year license. Organizations can try Nessus Pro free for seven days.
Intruder scans your IT environment to find a variety of vulnerabilities, including misconfigurations, missing security patches, and application bugs. The platform makes vulnerability management simple with threat prioritization and actionable remediation advice that IT and business stakeholders can understand.
IT teams can track how long it takes their organization to remediate vulnerabilities with Intruder’s Cyber Hygiene Score. Scores are determined by the time it takes to fix issues, which is benchmarked against targets set for critical, high, medium, and low-level vulnerabilities. You can quickly retrieve this information from your dashboard, which displays your performance over six months and the average time to fix each issue type.
Intruder users have access to multiple integrations, including AWS, Google Cloud, GitHub, and ServiceNow.
Pricing is based on the number of assets your organization needs to scan. A free 30-day trial is available for Intrudor Pro.
Imperva
Enterprise-grade cybersecurity solution that guards against complex DDoS attacks
Enterprises use Imperva’s cybersecurity solutions to protect their applications, data, and networks. The web application security suite is Imperva’s specialty, offering firewalls and advanced bot, client-side, and runtime protection. Imperva also uses machine learning to spot suspicious behavior, enabling security teams to stop and contain attacks early.
DDoS protection is one of Imperva’s top features. The system proxies all your incoming traffic to block layers 3, 4, and 7 DDoS attacks before they reach your servers. Whether your applications are in the cloud or on-premises, Imperva DDoS Protection is constantly monitoring your assets to ensure business continuity and minimal downtime in the event of an attack.
Imperva integrates with leading SIEM tools, including ArcSight and Splunk.
Multiple protection plans are offered for applications and data. Pricing is available upon request.
The Best Vulnerability Scanning Software Solutions Summary
| Tools | Price | |
|---|---|---|
| Intruder | From $196/month/application | Website |
| Astra Pentest | From $99/month | Website |
| ESET PROTECT Complete | Pricing upon request | Website |
| Qualys | From $542/month | Website |
| Acunetix | Pricing available upon request | Website |
| Microsoft Baseline Security Analyzer | No price details | Website |
| Invicti | Available upon request | Website |
| Tenable | $3,390/Year License | Website |
| Intruder | From $157/month/1 application | Website |
| Imperva | No price details | Website |
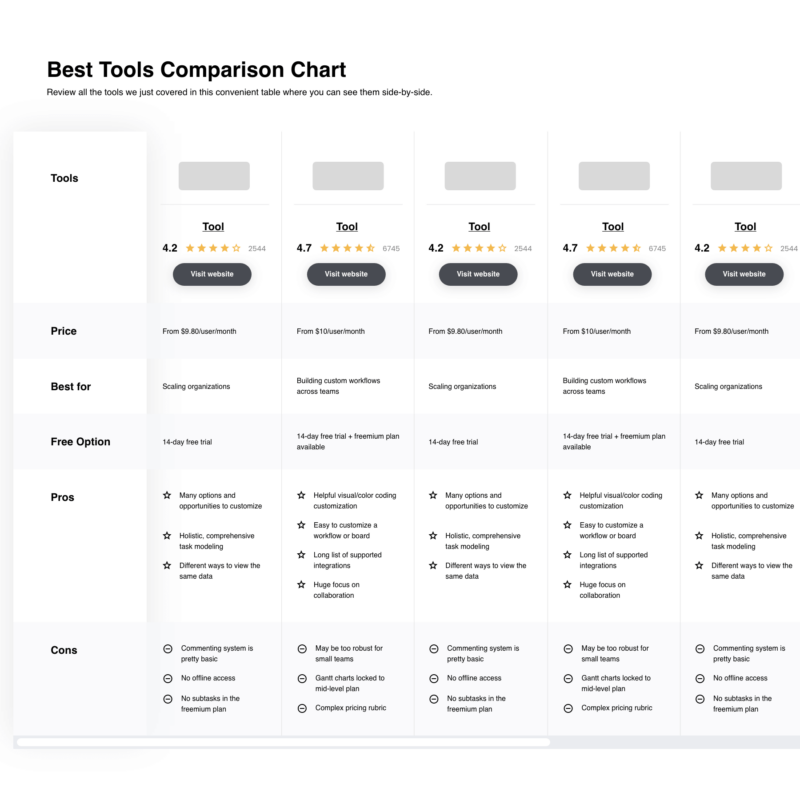
Compare Software Specs Side by Side
Use our comparison chart to review and evaluate software specs side-by-side.
Compare SoftwareOther Options
Here are a few more vulnerability scanning tools that didn’t make the top list.
- Probely
Web app and API vulnerability scanner that’s easily accessible to developers
- Rapid7
Offers external threat intelligence solution with clear and dark web monitoring
- Burp Suite
Vulnerability scanning tool great for crawling JavaScript-heavy applications
- Cyberpion
EASM solution with multi-layer vulnerability assessment engine
- beSECURE
Leading provider of governance, risk, and managed security solutions
- New Relic
Best vulnerability scanning software to lower the rate of false positives
- GFI Languard
Network security software with patch management tool
- NMap
Open source utility for asset discovery and security auditing
- Frontline Vulnerability Manager
SaaS vulnerability management solution for network systems and software
Comparison Criteria
The criteria below will help you decide which vulnerability scanning software tool is best for your business.
- User Interface (UI): A simple, user-friendly interface helps security analysts configure a vulnerability scan quickly and accurately.
- Usability: Good usability makes vulnerability scanning tools accessible to security experts and developers. Increased access enables software teams to implement security testing earlier in the development lifecycle.
- Integrations: The best vulnerability scanners offer a variety of plug-ins and integrations that easily connect with your existing SIEM and CI/CD tools.
- Value for $: The cost of your scanning tool should match the value it brings to your security efforts.
Vulnerability Scanning Tools: Key Features
These key features ensure your vulnerability scanning tool provides the best protection against threats.
- Asset Discovery: To protect your IT environment, you must know which assets are connected to the network. The top scanning tools can detect known and unknown assets that pose a high risk to your organization.
- Threat Intelligence: There are countless cyber threats across the clear, deep, and dark web. Select a scanning tool that provides the latest threat research you need to mitigate attacks.
- Automation: You can send secure products to market faster with scanning tools that automate your security team’s pre- and post-scan operations.
- Threat Prioritization: Your scanning software should help you triage threats, enabling you to quickly contain security issues that pose the highest risk to your business.
What do you think about this list?
Check out other software testing tools to help your team build more secure products. Sign up for our newsletter for the latest insights from top thinkers in the QA industry.
Related List of Tools: BEST SQL EDITORS & HOW TO CHOOSE THE RIGHT ONE




















