Network penetration testing is a vital part of today's information security architecture. Its importance has grown as the sophistication of data breaches over the years has grown, underscoring the need to fortify information security systems. The National Vulnerability Database (NVD) of the United States’ National Institute of Standards and Technology (NIST) recorded a total of 180,532 vulnerabilities in 2020 alone.
Penetration testing helps expose these vulnerability flaws in a system. This security test is done by the good type of hackers known as ethical hackers. This qualifier is necessary because hacking used to have a negative, countercultural connotation. Growing up as an impressionable kid, one of the things that drew me into IT was the allure of the renegade hacker portrayed in movies and television.
One of my favorites is "Catch Me If You Can," mainly because it chronicled the real-life exploits of the skilled forger, Frank Abagnale, Jr. who reportedly became the most successful bank robber in history by the age of 17.
More pertinently, the movie highlights the importance and lessons of various penetration testing concepts.
Penetration Testing: To catch a thief, you need to think like a thief
Technically, Frank wasn't a hacker but his genius for discovering and exploiting vulnerabilities in a system parallels the approach used by both ethical and malicious hackers.
More so, the battle of wits between Frank and the FBI agent on his pursuit, Carl Hanratty, mirrors the cat-and-mouse game between malicious actors and the cybersecurity professionals tasked with our defending digital fortresses.
Penetration testing simulates the process and methods a hacker uses or would utilize to compromise a system. Just like Agent Hanratty, ethical hackers need to anticipate and think in the same nefarious patterns followed by the bad guys.
While ethical hackers play a vital role in network penetration testing, the tools they use are equally important. If you're using Jira for project management, you might find our guide on test management tools for Jira beneficial for streamlining your ethical hacking efforts.
Penetration Testing: The best offense is always a strong defense
Frank eventually found redemption by becoming a respected authority on cybercrime, scams, forgery, and secure documents. He channeled his original pursuit of crime into helping banks identify vulnerabilities in their system.
Network penetration testing seeks to accomplish the same purpose of closing security vulnerabilities to help organizations protect sensitive data. Thus, ethical hackers and ethical hacking play a vital role in today's cybersecurity landscape.
But those who guard information in our digital age face an environment where the balance of power is already stacked against them.
"To safeguard the IT infrastructure entrusted to them, cybersecurity experts have to be right all the time. A hacker, on the other hand, only has to be right once."
This difficulty of playing defense is compounded by the lack of IT professionals with appropriate expertise and experience. According to Forbes, there are 465,000 unfilled cyber jobs across the United States alone.
Network penetration testing is, at least, a step in the right direction.
This article will cover the following topics:
- What Is A Network Penetration Test?
- Network Penetration Testing Types
- Who Is Typically Responsible For Conducting A Penetration Test?
- 4 Step Guide To Running A Successful Penetration Test
What Is A Network Penetration Test?
A network penetration test (also called a pen test) seeks to identify vulnerabilities in a software system by simulating a cyber-attack. This simulated attack also tests the resilience of an organization's information security by gauging its ability to withstand a breach or compromise.
To achieve this, white hat or ethical hackers intentionally deploy the methods and techniques used by malicious agents. But in this case, to uncover and subsequently fix security weaknesses or flaws in the system's security profile.
Although the purpose is to compromise a system, ethical hackers need to have lawful and authorized access. So, a pentester needs to have a documented mandate or authorization from the organization to allow the ethical hacking exploits to proceed.
Ultimately, the results allow network and cybersecurity professionals to provide recommendations that'll improve the network and overall security of the organization against future attacks.
In addition to network-layer assessments, pen-testing also encompasses application-layer tests, along with remote access vectors like VPN connections.
The pen test typically has the two primary goals:
- To determine whether malicious hackers can gain unauthorized entry into a system, how they might go about subverting its security defenses to achieve this purpose, and the subsequent impact of those activities on system logs, files, customer data, and/or intellectual property.
- To determine whether security measures and controls such as vulnerability management, are in place to fortify the security of the IT infrastructure.
A pen test is a tremendous way to learn and understand a company's risk posture. It allows an organization to establish if their digital assets can be compromised, and if so, to subsequently classify the risks the threats posed to their overall cyber security.
Here are some of the additional benefits of conducting a penetration test:
- Preventing the occurrence of network and data breaches
- Understanding and establishing the network baseline
- Testing security controls and components
- Safeguarding system and network security
Network Penetration Testing Types
There are several ways to approach penetration testing. In terms of testing the overall security infrastructure of an organization, it can be done from two perspectives, namely through internal or external methods.
- Internal network penetration testing: This test helps to evaluate the damage attackers can cause when they initially gain entry into the network. The purpose of internal tests is to both mirror insider threats within the corporate perimeter, and gauge the extent of malicious or inadvertent actions that lead to the compromise of information assets.
- External network penetration testing: These tests probe the effectiveness of a network's perimeter defenses. It tests the capability of external security controls to both detect and prevent attacks.
Another type of approach used to categorize penetration testing is based on the degree of information provided and the level of knowledge available to the tester.
- White box testing: This is the most refined testing approach because it allows testers to verify and inspect the innermost workings of a system. Hence, white box hackers are provided with as much knowledge of the system as possible.
- Black box testing: Here, the ethical hacker starts with a minimal level of knowledge. This type of test is used to simulate brute-force attacks since the hacker is unaware of the complexity of the inner workings of the infrastructure being targeted.
- Gray box testing: This is a compromise between the two other testing extremes. So, the test team is provided with partial knowledge of the system.
Penetration tests can also be classified based on their components and attack vectors.
- Social engineering: This is human-focused and thus represents one of the weakest links in a business's cybersecurity. It is commonly perpetrated using email phishing.
- Network infrastructure testing: This test interrogates the network for gaps and vulnerabilities that can be exploited across internal and external access points. They typically target network areas like firewall bypass testing, IPS deception, and DNS level attacks.
- Wireless network testing: This test exploits unprotected wireless networks by exposing vulnerabilities and evaluating the potential damage that could be caused.
- Web application security testing: This targets flaws in application logic and session management to execute exploits like SQL injection attacks.
Who Is Typically Responsible For Conducting A Penetration Test?
Penetration tests are carried out by ethical hackers who have been granted the authorization to carry out simulated attacks on the web application or network security of an organization. Legal permission is necessary as pen testing is often conducted by third parties who offer penetration testing services.
The penetration testers who seek to breach a system are on what is called the red team. Those operating on the red team are offensive security professionals responsible for testing the organization's defenses. The red team identifies attack paths that can be used to compromise its security and expose its vulnerabilities, using real-world attack techniques.
On the other hand, the blue team is comprised of cyber professionals concerned with security defense mechanisms. In practice, they defend against the red team and maintain internal security defenses against cyber-attack threats.
4 Step Guide To Running A Successful Penetration Test
As a systematic exercise, a penetration test requires standardized methodologies and frameworks to be conducted effectively. Penetration testing typically follows tried and true methods to address the presence of real or potential vulnerabilities in an application system.
Four main steps are typically involved in executing a successful network penetration test.
Step 1: Information gathering and determination of scope
The information-gathering phase normally occurs at the beginning of the security testing exercise. However, it can also be an iterative and self-reinforcing process, occurring throughout the network penetration test as successful intrusions yield more information about the target.
Here, security professionals and test experts engage with the organization to identify and do an accounting of all network assets such as firewalls and other devices.
The information-gathering process includes scoping and clarifying the client's expectations.
Penetration Testing Scope
To be successful, penetration testing has to be a disciplined, focused activity. This is because it might not be practically or financially feasible to examine the entire perimeter of an IT infrastructure. As a result, an important part of the information gathering stage involves determining the scope of the penetration test.
Scoping is a summation of all the boundaries and perimeters of engagement that the security team will explore during the testing process. So, the scope of a test determines its level of intrusion, and scoping is when the boundaries of engagement for the pen test are delineated.
Due to time constraints and other practical reasons, some areas of the system, such as its connected devices, might be excluded during testing.
Step 2: Reconnaissance and discovery
To understand how to fix vulnerability loopholes, ethical hackers have to perform detailed reconnaissance. This is especially necessary for black-box pen tests, where ethical hacker has to find the information they need to exploit vulnerabilities by themselves.
Reconnaissance and discovery are exploratory mechanisms used to survey the overall security infrastructure of an organization. This phase allows security experts to covertly scout the resources and security posture of their target.
Active Reconnaissance Tools
Active reconnaissance involves directly probing and engaging with the target system to get an actionable response.
To successfully conduct a network penetration test, it is crucial to understand the key techniques and tools needed to perform such reconnaissance. Here are some of the tools used to execute penetration tests:
- Port scanning: This is a popular reconnaissance method used to determine the open ports on a system. Port scanning enables a pen tester to determine the strength of the network security and the services running on a machine. This tool reveals which ports are open and receiving information (listening) in addition to facilitating fingerprinting. Fingerprinting a network allows the user to discover security devices like firewalls between the sender and the target. Stealth port scans that can go undetected in a system's log files are of prime interest to hackers.
- Examples of port scanning tools include Nmap or Network Mapper, TCP Port Scanner, Port Authority, NetScanTools, and so on.
- Packet sniffing: These tools allow you to detect and observe the data packets flowing across a network. Packet sniffing tools are also known as packet or network protocol analyzers. Network administrators use these tools to monitor their networks to detect spoofed packets, stray IP addresses, and suspicious packet generation from a single IP address. But hackers use them to search for vulnerable network services such as ports and protocols and to implement man-in-the-middle attacks.
- Examples of packet sniffing tools include Wireshark, Nmap or Network Mapper,
- Ping sweeping: Ping sweeps are used to establish a range of IP addresses which map to live hosts. This network scanning technique can ping multiple network addresses simultaneously. A hacker uses this network probe to send a set of ICMP ECHO packets to servers in order to see which ones respond. This enables them to determine which ones are live.
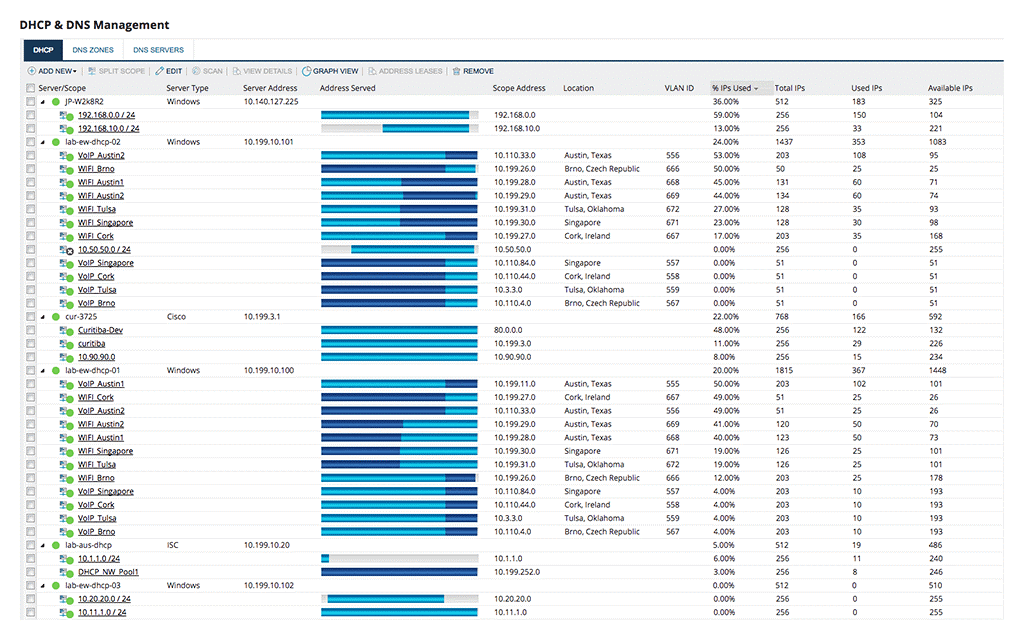
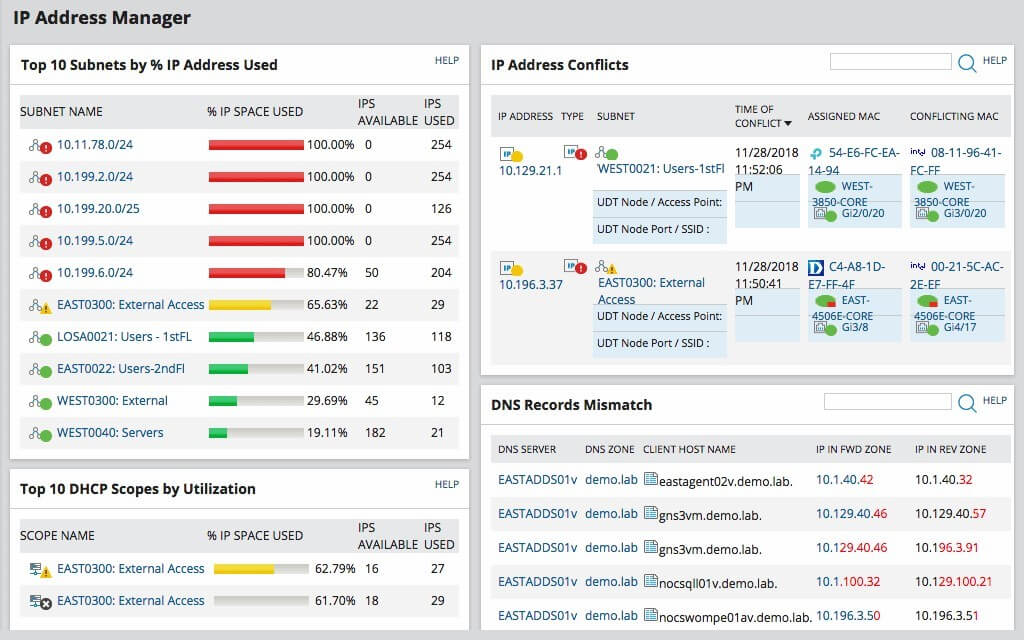
- Examples of ping sweep tools include SolarWinds IP Address Manager (IPAM), ManageEngine OpManager, and PingPlotter Pro.
- Vulnerability scanning: These involve tools used to identify configuration problems and other known vulnerabilities in networks and network hosts such as the presence of malware. However, you need to understand the differences between penetration testing and vulnerability scanning.
- Examples include Nessus, Acunetix, Nexpose, and many others.
- Web application security testing: These tools are invaluable for testing the security of web applications at every phase and discovering weaknesses in their configuration. Methods like static and dynamic analysis are used to discover vulnerability in software code of applications.
- Integrated platforms like Burp Suite bundle several applications for testing and securing web applications with tools like advanced web application scanners, intercepting proxy, intruder tool, and sequencer tool.
- Social engineering and Internet information queries: Social engineering attacks are primarily used to surreptitiously gain access to information systems by tricking users to provide their login credentials.
Discovery is the logical consequence of a successful reconnaissance. When you discover and identify a path to breach the network, you step into action to exploit those security risks.
Step 3: Exploitation, execution, and escalation
The next step in penetration testing is the actual exploitation of the weaknesses discovered in the information security systems during reconnaissance. The objective of this phase is to see how far the ethical hacker can gain entry into the system without detection.
These simulated attacks occur in a controlled environment where the tester either chooses the easiest attack vector or the most critical exploit based on intelligence gathered during reconnaissance. Some of these attacks include SQL injection, cross-site scripting, buffer overflow, escalation of privileges, and so on.
The most common framework used to configure the exploit to be targeted and payload to be used at this stage is Metasploit.
Once the attacker has gained a foothold inside the system, they can pivot and move deeper inside it to compromise other assets like vulnerable Linux or Windows operating system machines.
Step 4: Reporting and remediation
After the penetration test has concluded, the tester(s) should compile a report of the findings for the organization. The report should include details of the process, the vulnerabilities discovered, evidence collected, and recommendations for remediation.
Remediation involves the important process of closing the security gaps uncovered during the testing process. This should prompt a robust discussion on the most effective means of remediation that best mitigates each of the vulnerabilities discovered.
Remediation might encompass a wide range of actions such as:
- Implementing software patches and updates
- Implementing configuration or operational changes
- Developing and introducing new security measures, procedures, and tools
Fortify Your Network With Penetration Testing
The goal of penetration testing is to make your network and information security system more secure by allowing security consultants to probe and evaluate their effectiveness. Once those weaknesses have been exposed, the onus is on the organization to mitigate the risks that have been identified.
Subscribe to The QA Lead newsletter to learn more about end-to-end testing built for scale.
Related Reads:
Also Worth Checking Out:
- MODERN QUALITY ENGINEERING: HOW TO REDEFINE QUALITY STRATEGY FOR AGILE FRAMEWORKS
- WHAT IS TESTGEAR? OVERVIEW & TOUR OF FEATURES
Related List of Tools: