10 Best Vulnerability Management Tools Shortlist
Here's my pick of the 10 best software from the 16 tools reviewed.
There are seemingly countless vulnerability management tools available, so figuring out which is best for you is tough. You want to maintain the security and integrity of your IT systems but need to figure out which tool is the best fit. I've got you! In this post I make things simple, leveraging my experience using dozens of different vulnerability management software to bring you this shortlist of the best vulnerability management tools.
What are Vulnerability Management Tools?
Vulnerability management tools are software that help organizations identify, assess, and mitigate vulnerabilities in their IT systems and networks. These tools scan for security weaknesses across various digital assets, including networks, applications, and databases. They systematically evaluate potential risks and provide information necessary for addressing them.
The benefits and uses of vulnerability management tools include enhanced cybersecurity by proactively identifying and addressing potential security gaps. They aid in reducing the risk of data breaches and cyber attacks, ensuring compliance with security standards and regulations. These tools prioritize vulnerabilities, allowing organizations to focus resources on the most critical issues, improving overall IT security posture. They also provide valuable insights into the organization's security vulnerabilities, facilitating informed decision-making and strategic planning in cybersecurity measures.
The 10 Best Vulnerability Management Tools
The following overviews highlight information from my selection criteria above, links to that tool provider’s website, and standout features users like myself find especially valuable. You’ll also find details on plan pricing, pros and cons, and whether a free plan and/or trial are available.
Best for identifying potential security weaknesses across an organization's network
ESET PROTECT Complete is a cloud-based security solution designed for businesses looking for comprehensive protection across their IT environment. It includes features such as antivirus, software update settings, personal firewall, web and email scanning, device control, and mobile device management.
As a vulnerability management software, ESET PROTECT Complete proactively scans your networks using AI technology to identify potential security weaknesses. The platform will flag issues in detailed reports and provide practical steps for remediation. You'll have full control and visibility of your network's security monitoring within a single dashboard.
Furthermore, the tool offers multi-layered protection that extends beyond traditional endpoints, safeguarding virtual environments, cloud applications, and mobile devices. The software's compatibility with a range of operating systems and platforms ensures you can maintain robust security across your entire digital infrastructure. Additionally, ESET's commitment to minimal system impact ensures that security measures do not impede performance, allowing your business to operate efficiently while maintaining high-security standards.
Integrations include ConnectWise Automate, Datto RMM, NinjaOne, Kaseya VSA, ATERA, and more.
New Relic is an all-in-one observability platform that helps you monitor, troubleshoot, and tune your full stack. It's like having a super-smart, all-seeing eye on your software, helping you spot and fix issues before they become big problems.
I picked New Relic because of how easy it is for you to see all of the vulnerable entities and libraries across the estate you are responsible for. The vulnerability dashboard lets you see an overview of what is going on and you can drill down into the details with a few clicks. Inside each entity, you will find a vulnerabilities section that lists all the anomalies that have been detected. You can then go into each one and find specific details about this vulnerability and even suggestions on how to resolve it.
Now, if you are an app owner or developer, you can get help from New Relic on how to prioritize your work. The platform's vulnerability triage feature gives you information based on criticality. Then, it displays a prioritized list of your vulnerable libraries as well as suggestions on which libraries to update to.
New Relic integrates with over 600 applications within the categories of application monitoring, infrastructure, security, traffic simulation, logging, AWS, Azure, Google Cloud Services, open-source monitoring, machine learning ops, and Prometheus.
UnderDefense MAXI is a security and compliance automation platform that offers 24/7 business protection. Its vulnerability management software is designed to enhance digital security and resilience so you can identify, assess, and mitigate potential risks within your network.
As a vulnerability management software, UnderDefense MAXI can identify risks early with real-time threat detection. Using human-led, AI-assisted protection, the platform automatically monitors external threats, like leaked credentials, network misconfigurations, and dark web mentions, and provides actionable alerts for better decision-making.
The platform also provides a 24/7 concierge team for continuous protection and support, ensuring a well-rounded approach that offers the efficiency of AI and the expertise of a cybersecurity team so you can detect and mitigate vulnerabilities early.
Features include advanced threat detection, vulnerability management and monitoring, compliance assessment, a 24/7 concierge team, and more.
Integrations include Splunk, SentinalOne, Radar, AWS, Microsoft, GCP, Kubernetes, SIEM, EDR, Office 365, Google Workspace, and many more.
Intruder is a cloud-based vulnerability scanner designed to help small and medium-sized businesses proactively identify and address security weaknesses in their digital infrastructure. By offering continuous scanning, effortless reporting, and proactive threat response, the platform positions itself as a leading solution for SMBs seeking to maintain robust security postures.
I selected this software because it provides a comprehensive view of an organization's attack surface, combining continuous network monitoring with automated vulnerability scanning and proactive threat response capabilities. What distinguishes Intruder is its focus on delivering not just information regarding threats, but also how to address them. Scan results come with accompanying instructions on how to resolve issues.
The software integrates natively with Slack, Microsoft Teams, Jira, Github, and Gitlab. Other integrations can be accessed through Zapier and API.
Paid plans start from $196 per month, per application. A 14-day free trial is also available.
Qualys
Offers lightweight container security solution for DevOps teams
Qualys Vulnerability Management combines lightweight cloud agents, virtual scanners, and network analysis to deliver global visibility and protection to your IT assets. The system was designed for hybrid IT environments with the capability to identify known and unknown assets on-premises and in the cloud with its Global AssetView application. Your security team will receive real-time alerts on zero-day vulnerabilities, compromised assets, and network irregularities.
DevOps teams can also utilize Qualys to monitor and protect container applications. Qualys Container Security (CS) detects vulnerabilities and compliance issues in container-native applications on AWS without disrupting continuous integration and delivery. Along with detecting vulnerabilities, Qualys CS also enables developers to control which container images are deployed and automatically enforce normal application behavior.
Qualys offers native integrations with Splunk, ServiceNow, and several DevOps tools, including Puppet, Jenkins, and Bamboo.
Pricing is available upon request. Teams can also try Qualys free for 30-days.
Automatic scanning ensures endpoints have up-to-date antivirus protection
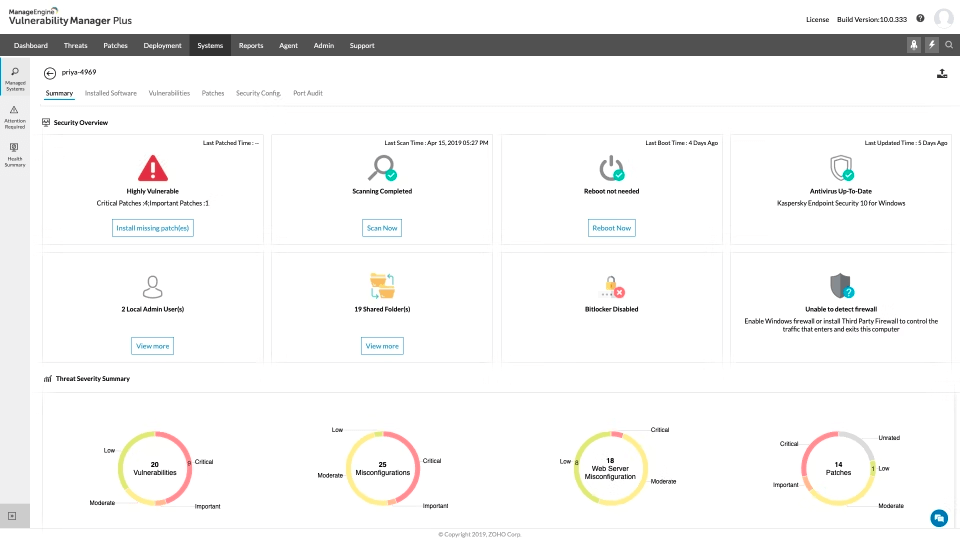
ManageEngine Vulnerability Manager Plus is an enterprise vulnerability management and compliance solution. The tool provides comprehensive coverage of threats and vulnerabilities for endpoints on local, DMZ, and remote networks. Vulnerability Manager Plus also offers more than 75 CIS benchmarks to help security teams maintain secure baseline system configurations.
Malware and viruses can attack enterprise networks from a thousand angles. With Vulnerability Manager Plus, all of your endpoints are automatically scanned to determine if antivirus software is present. The system also determines if your antivirus protection is up-to-date with the latest antivirus definitions. Users can deploy antivirus definition updates directly from the platform to Windows Defender Antivirus and McAfee VirusScan Enterprise.
Pricing for Vulnerability Manager Plus Enterprise Edition starts at $1,195 for 100 workstations and a single-user license. Custom pricing is also available.
Cloud-based endpoint security solution with pre-built remediation workflows
Syxsense is a cloud-based endpoint management and security solution for small to medium-sized businesses and large enterprises. The tool’s security scanner actively monitors for blacklisted software, hashes, and threats across all your managed devices. Syxsense’s AI capability helps security teams stay ahead of attackers by predicting vulnerabilities before they occur.
Distributed IT teams can protect their organization’s network from anywhere by automating security patches from the cloud. Teams can automatically deploy patches for operating systems and third-party applications. Syxsense also automates Windows 10 feature updates.
Threat remediation is also simplified through the Syxsense Cortex Remediation Workflow library. It features over 100 pre-built and pre-tested remediation workflows for common vulnerabilities. Security teams can simply review the pre-built remediation workflow and approve it for deployment.
Syxsense’s Open API lets you easily integrate and share data between the platform and your existing security and IT solutions, including helpdesk and asset management applications.
Pricing starts at $600/year for ten devices.
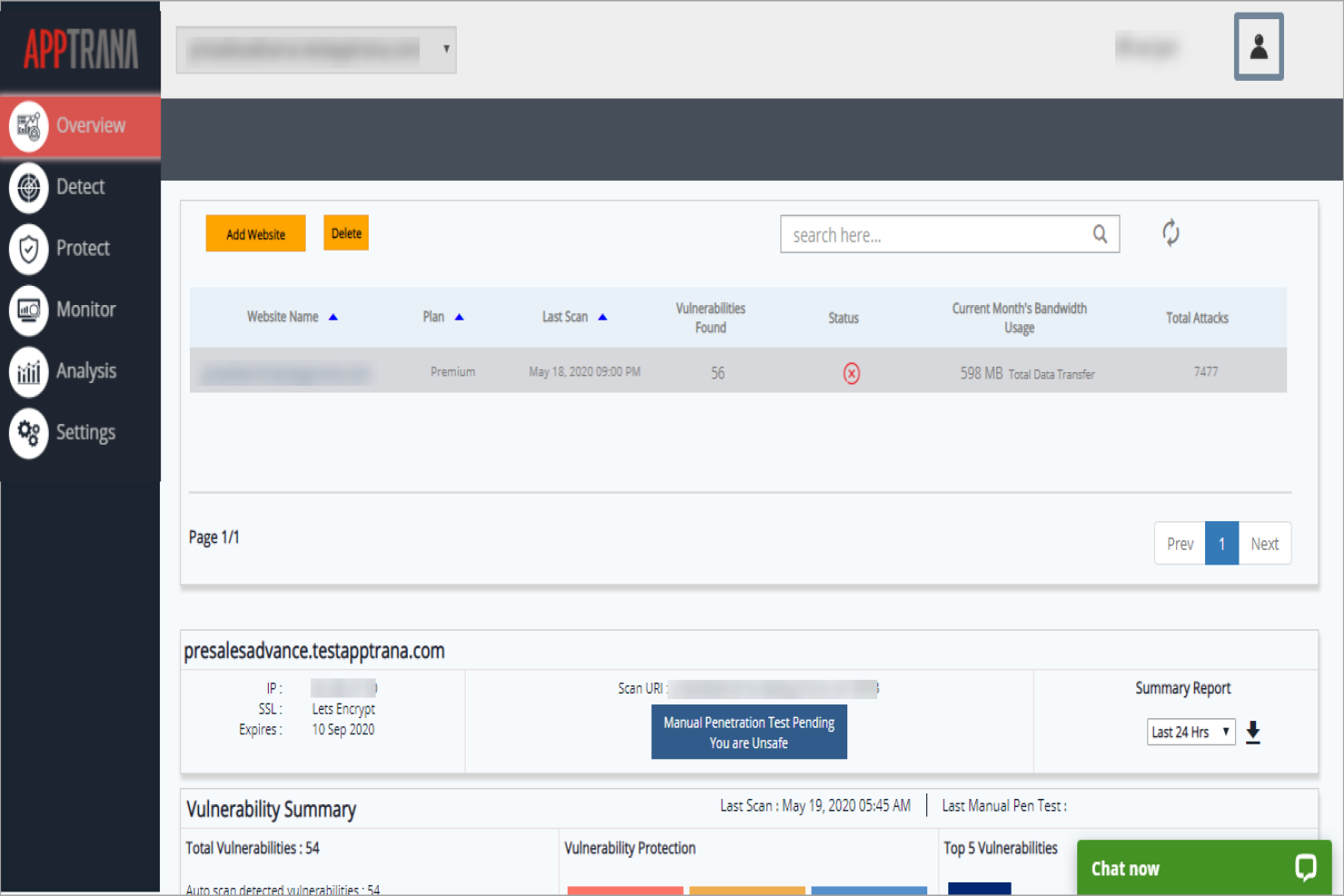
AppTrana
Best vulnerability management service for enterprise organizations that fully managed
AppTrana is a vulnerability management tool for penetration testing, behavioral-based DDoS protection, mitigating bot attacks, and defending against the OWASP top 10 vulnerabilities. Enterprise organizations employ the tool to service all large-scale vulnerability management needs.
Why I picked AppTrana: the tool is a fully managed security solution, which means that their web security expert team analyzes and updates security policies, reducing the in-house strain of servicing these critical functions.
The service enables you to secure your applications without worrying about their day-to-day management. The fully managed security service works as your extended team to meet your security needs and can be scaled based on your growth. The service also utilizes an application firewall that takes a risk-based approach to identify and patch vulnerabilities, providing tailored protection to applications.
AppTrana Standout Features & Integrations
Features include unlimited application security scanning, manual pen-testing of applications, DDoS mitigation, bot management, managed CDN, false positive monitoring, custom SSL certificates, and risk-based API protection.
AppTrana Plans & Pricing
AppTrana pricing starts at $99 per month per app. A free 14-day trial is available.
F-Secure
Best vulnerability management tool for device protection against viruses, ransomware, and malware
F-Secure is a vulnerability management tool that allows organizations to monitor and address malware issues. The tool boasts a simple and detailed user interface that makes it easy to navigate and review the results of a vulnerability scan.
Why I picked F-Secure: the tool focuses on defending your entire system against malware and ransomware, allowing you to ensure your system's security is fully covered. As some of the most vulnerable aspects of your system are your organization's employee devices, protecting them ensures you can manage vulnerability threats effectively,
The tool allows you to choose from various scan options starting with a simple quick scan all the way to a full computer scan. You can also set the particulars of the scan you wish to execute.
F-Secure Standout Features & Integrations
Features include access to VPN services, customer support, identity monitoring, kill switch, password manager, antivirus functions, browser protection, and more.
Integrations include all major OS systems such as macOS, Windows, Android, and iOS.
F-Secure Plans & Pricing
The cost of F-Secure starts at $67.49/per month for up to 3 devices. The tool also offers a 30-day free trial and freemium service.
Multi-layered security suite featuring DNS over HTTPS traffic filtering tool
Heimdal Security simplifies IT operations and security by combining threat prevention, vulnerability management, and antivirus into one platform. The tool stops the most sophisticated cyberattacks on day one, including ransomware and insider threats. Heimdal’s Patch & Asset Management software enables security teams to automatically deploy and patch any Microsoft and Linux operating system and third-party and proprietary software.
Advanced threat hunting is provided through Heimdal’s Threat Prevention solution. Threat Prevention protects organizations from hidden malware and other exploits of legitimate network assets and cloud services. Security teams can threat hunt beyond the limits of DNS by leveraging DNS over HTTPS traffic filtering to spot malicious URLs and activity.
Pricing for each Heimdal product is available upon request. Teams can also try Heimdal for free.
The 10 Best Vulnerability Management Tools Summary
| Tools | Price | |
|---|---|---|
| ESET PROTECT Complete | Pricing upon request | Website |
| New Relic | From $49/user/month | Website |
| UnderDefense | Pricing upon request | Website |
| Intruder | From $196/month/application | Website |
| Qualys | From $542/month | Website |
| ManageEngine Vulnerability Manager Plus | $1,195 for 100 workstations and a single-user license. | Website |
| Syxsense Manage | $600/year for ten devices | Website |
| AppTrana | $99/month/app | Website |
| F-Secure | $67.49/per month/ up to 3 devices | Website |
| Heimdal Security | No price details | Website |
Compare Software Specs Side by Side
Use our comparison chart to review and evaluate software specs side-by-side.
Compare SoftwareOther Options
Here are a few more vulnerability management systems that didn’t make the top list.
- GFI Languard
Vulnerability management solution with extensive threat database
- Rapid7
Leverages open data research to discover external-facing assets
- Kenna Security
Utilizes data science to deliver highly accurate risk prioritization
- SecPod SanerNow Cyberhygiene Platform
Best vulnerability management tool for automating cyber hygiene operations
- Tenable
Provides benchmarking dashboards to compare cyber exposure against industry peers
- Tripwire
Automated vulnerability management software for IT and OT environments
How I Picked the Best Vulnerability Management Tools
To decide which tools to feature in this list, I evaluated and compared the details for several popular vulnerability management tools. I weighed various key factors and functions that would be top of mind for businesses of all sizes.
Below is the selection criteria I used to review the most effective vulnerability management tools available on the market.
- User Interface (UI): A responsive interface makes navigating vulnerability management tools simple.
- Usability: Good software usability ensures security teams can quickly adopt new tools without extensive training.
- Support: Knowing you can rely on dedicated support resources can maximize the value potential a tool brings to your organization.
- Integrations: Access to various integrations means you can easily add new security solutions to your existing CI/CD pipeline without disrupting productivity.
- Licenses and Pricing: The best vulnerability management tools are cost-efficient and highly effective at securing your IT environment.
People Also Ask: Vulnerability Management 101
Why Vulnerability Management is Important
An organization’s security posture is only as strong as its ability to recognize and reduce risk. Along with security and test experts, vulnerability management tools enable an organization to monitor and defend attack surfaces from external threats proactively.
Key Features of Vulnerability Management Tools
- Automated asset detection: Asset detection provides security teams with full visibility into their attack surface.
- Patch management: Patch management tools typically utilize automation to simplify deploying updates to your software.
- Vulnerability Scanning: Vulnerability scanning tools help proactively identify weak points in a system, software, or server to address malicious activity.
- Remediation guidance: Remediation guidance takes the guesswork out of finding the right solution to fix critical vulnerabilities.
- Real-time dashboards: Real-time reporting speeds up threat detection and response.
Related Tools
- Best Test Management Tools
- 5 Main Stages Of The Vulnerability Management Process
- Best Software Development Tools
- Best Vulnerability Scanning Software QAs Are Using
So How Can You Maximize the Value of Vulnerability Management Tools?
Vulnerability management is an essential function of any software testing process and management. Learn about other software testing tools that can help secure your IT infrastructure and get the latest insights from QA experts by subscribing to our newsletter.